// htb writeup
Hack The BoxhttpsapphacktheboxcommachinesSoulmate
2026-02-25
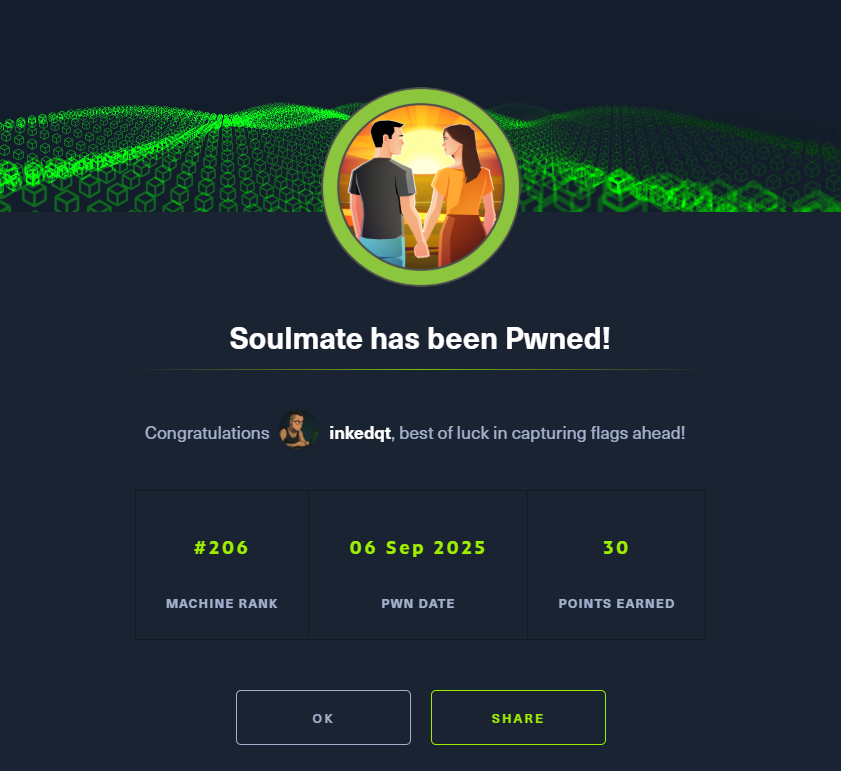
Soulmate
Soulmate — Hack The Box
📌 Overview
Machine Name: Soulmate
Difficulty: Easy
OS: Linux
Status: Active ✅
Platform: Hack The Box
🧩 Summary
Soulmate combined a CrushFTP exploit with custom Erlang components for an interesting and layered attack path. After discovering ftp.soulmate.htb, we leveraged CVE-2025-31161 to create an admin user in CrushFTP and reset existing credentials. With RCE achieved via a PHP backdoor, we escalated to SSH access and finally abused a custom Erlang-based login service to execute system commands as root.
🛠️ Exploit Chain
Subdomain discovery → CrushFTP admin RCE → password reset → PHP webshell → SSH creds → Erlang shell → root
📂 Write-up
🔗 Full write-up once retired: Soulmate on GitHub
Author: inkedqt
Website: https://inksec.io