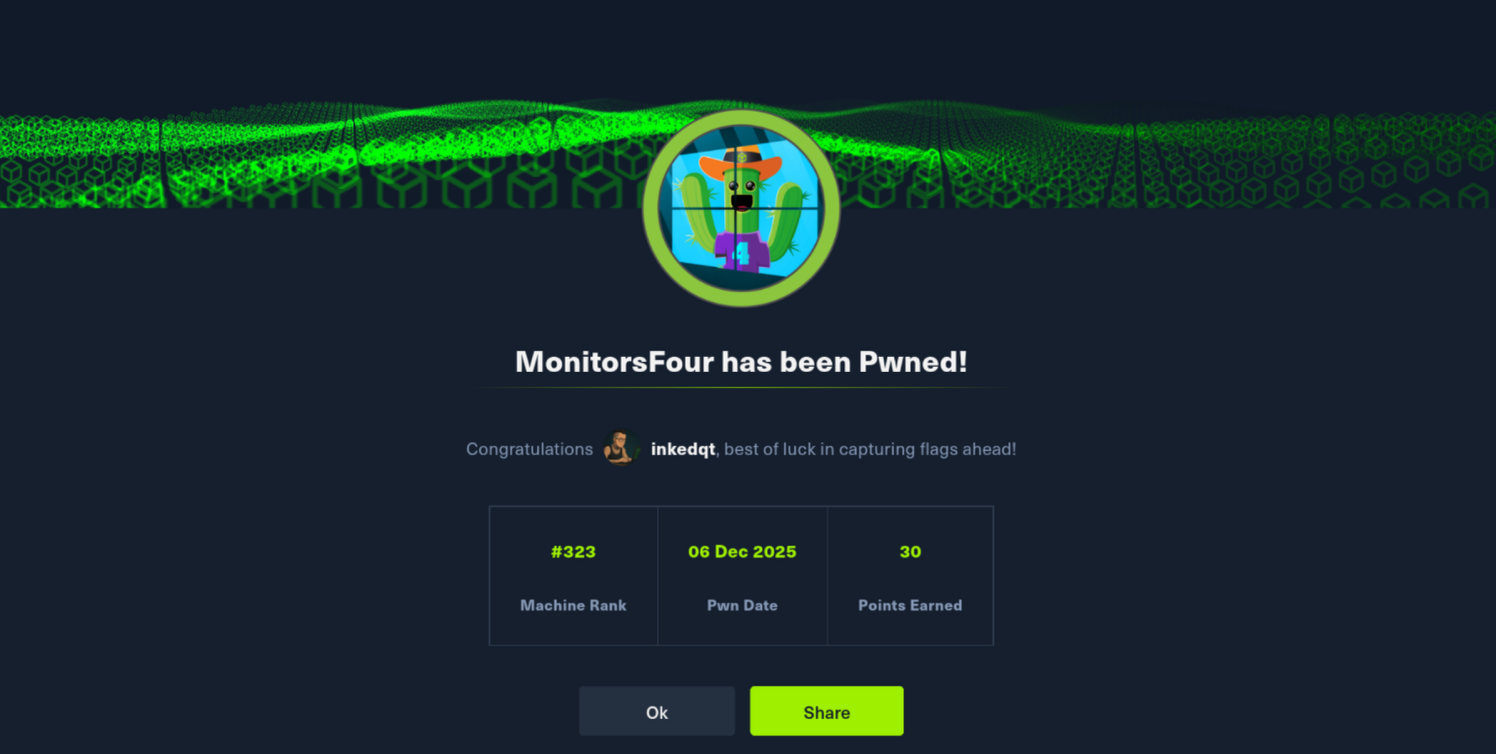
📊 MonitorsFour – HTB Seasonal (Season 9)
Status: 🔒 Private – writeup will be published once the machine retires Difficulty: Easy Platform: Windows Category: Web | Containers | Configuration Exposure | Privilege Escalation
🧠 Teaser
MonitorsFour starts exactly how many real incidents do: with configuration files that were never meant to be public.
A small web application leaks just enough information to undermine its own trust model, and from there the box becomes a lesson in how “minor” logic flaws cascade across services. What looks like a simple web issue quietly opens the door to administrative access elsewhere.
The final act shifts environments entirely. Once inside a container, the real question becomes how well the boundary between container and host is enforced — and in this case, the answer is “not very.”
🪛 Tools You’ll Want (High-Level)
🔍 Web application logic review
🧠 Understanding of PHP type handling
📦 Familiarity with containerised services
🔑 Credential reuse awareness
⚙️ Comfort reasoning about container-to-host boundaries
This box rewards curiosity over brute force.
✅ You’ll Need To:
🕵️ Treat leaked configuration as a first-class vulnerability
📦 Follow authentication logic rather than endpoints
🧠 Recognise how “safe” comparisons fail in dynamic languages
🔄 Pivot across services that share credentials
🔓 Escalate by abusing orchestration assumptions, not kernel bugs
🧠 Takeaways
• Configuration exposure is often more dangerous than code flaws.
• Type juggling bugs still matter in modern stacks.
• Containers are only as isolated as their management interfaces.
• “Easy” boxes can hide very real architectural failures.
MonitorsFour is a great reminder that real-world compromises often begin with something small — and end somewhere completely different.
📸 Proof